A Statista survey published in 2022 demonstrates that in the second quarter of 2022, internet users worldwide saw roughly 52 million data breaches. Unlike in movies, where we see a hacker compromising a computer system, data breaches are liable to happen on a large scale and usually require software or a toolbox that allows hackers to figure out credentials that are likely to work.
But how can data breaches happen so frequently and to such an extent? One of the feasible explanations is that user-generated passwords are vulnerable, allowing attackers to invade our privacy and sensitive information somewhat effortlessly.
However, passwordless authentication might be the key to fighting cybercrime, so let’s explore in greater depth how this technology can bolster user security.
What Is Passwordless Technology?
Passwordless technology or passwordless authentication describes a group of identity verification methods people can use to access an app or IT system. As the name says, passwordless technology doesn’t require users to rely on passwords. Instead, it allows them to depend on other identity confirmation evidence to access local or online services.

Photo illustration: Freepik
So, for example, some of the most common passwordless authentication methods include:
- USB token service
- One-time email verification
- App biometric authentication
- HOTP and TOTP (HMAC-based One-Time Password and Time-based one-time password)
- Persistent cookie
- One-time SMS password
But why is passwordless technology relevant for users?
In today’s world, we use dozens of apps and programs for work and entertainment alike, and according to Statista’s research from 2018, 45% of participants claim they use the same passwords for some online logins.
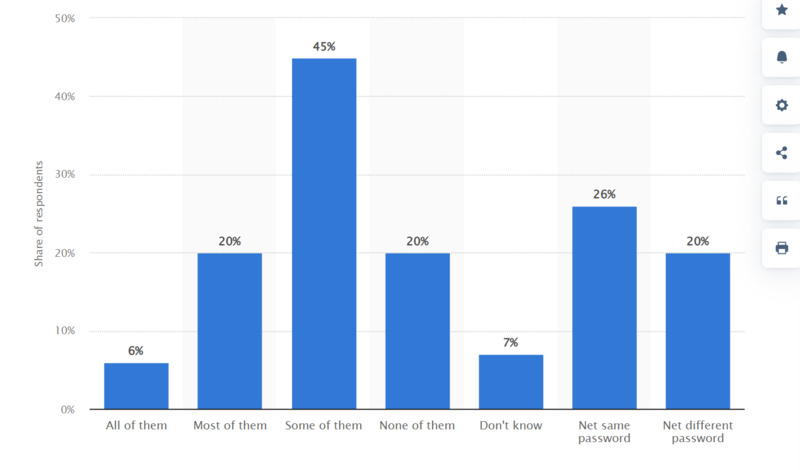
Source: Statista
Statista’s study clearly shows that there’s an undeniable chance that some people would suffer multiple data breaches due to their choice to keep their passwords’ versatility to a minimum. But who can blame them? We’ve all been in a situation where we couldn’t remember our password combination, so the least frustrating way is to use the same password for all accounts, right?
Although it may be the easiest method, it surely isn’t the safest. That’s one of the primary reasons many apps or IT systems require users to create strong passwords that include certain characters and symbols.
Then we have another problem. Can users remember all those strong passwords, and if not, what is the optimal solution? Here’s when passwordless technology can come in handy. If users could rely on other identity verifications without compromising security, data breaches are less likely to happen.
Is Passwordless Authentication the Future?
According to HelpNetSecurity, 94% of IT leaders are concerned about user-generated passwords. There’s no doubt that passwords have been the most popular authenticationmethod, but their nature is the primary cause of data breaches and identity theft.
Photo illustration: Freepik
A passwordless future means data breaches and identity fraud are far less likely, and the productivity and experiences of customers and employees are drastically improved. It's reassuring to see IT leaders across the globe aligned on a future where passwords are replaced by simple, easy, and more secure authentication.
Says Andre Durand, CEO of Ping Identity for HelpNetSecurity.
As state-of-the-art authentication methods emerge, people can improve account security and productivity. Once passwords are eradicated, users won’t have to go through a tiring process of looking up their complex passwords in a hidden folder and manually imputing the right combination to unlock account access. More importantly, their accounts will be more secure, as unique identity verification methods won’t be easy to breach.
For example, fingertip or facial recognition grants users account access in seconds. More importantly, as these verifications are unique to each user, the account security is far less likely to be compromised.

Photo illustration: Freepik
Of course, no technology is flawless, and many developers know that hackers can find vulnerabilities in this system. However, passwordless technology is far more reliable than the standard data string used to confirm a user’s identity.
What Is Passkey Technology?
In layman’s terms, passkeys are digital credentials for apps and user accounts that aim to replace old-fashioned passwords. In other words, users can rely on passkeys to authenticate without inputting a username, password, or another type of authentication.
This technology attempts to take the place of old-fashioned authentication methods like passwords. However, it’s worth noting that passkeys only work if the app or website in question enables them.
So, when users want to sign in to a service, their browser or OS will provide them with available passkey options. Then, the system will prompt the user to unlock their device to ensure that only the rightful owner can use a passkey. This could be done using a pattern, PIN, or biometric sensor (such as fingerprint or facial recognition).

Photo illustration: Freepik
Additionally, a user must register with a website or app that accepts passkeys to use them. So, the next time they want to access the service, they can:
- Open the app
- Click on the Sign in button
- Select their passkey of choice
- Unlock the device screen to complete the login
One positive side of using passkeys is that they don’t work only on devices where they are stored. With that in mind, users can create passkeys on mobile, only to use them to log in to their account via computer.
Still, availability across various devices isn’t the only positive aspect of passkeys. Some other benefits include the following:
- Protection against phishing
- Reduced risks of data breaches
- Reduced dangers of identity theft
Passkey vs Password: Which Is Better?
Both passwords and passkeys protect user accounts from prying eyes and unwanted third parties. But what’s the difference between them, and how can one be better than the other if they both have the same purpose?
As stated earlier, passwords pose a substantial risk to one’s security. A user may recycle or forget them. More importantly, they can be stolen. However, the stronger the password, the stronger is account security.

Photo illustration: Freepik
On the other hand, passkeys are the newest protection detail against data breaches that significantly reduce the chances of a cyber attack. They’re easier to use than passwords because a user doesn’t have to remember them. Instead, all they have to do to access their account is to confirm their identity via the fingertip of face recognition.
Many tech giants, including Google, recommend switching to passkeys. Unlike passwords, passkeys never leave your device, making them one of the best protection details against data breaches.
Some users may be surprised if a biometric authentication suddenly appears on a website or an app and think this is sending sensitive information to the server. With passkeys, the user's biometric information is never revealed to the website or the app. Biometric material never leaves the user's personal device.
Google Identity confirms.
How Do Hackers Get Passwords?
Hackers and scammers utilize various techniques to get a hold of people’s passwords and private information. Although some methods are more prevalent than others, they are all forms of cybercrime that leads to the exposure of sensitive information and, in some cases, identity theft.
- Phishing: Phishing is one of the most common ways a third party can access an account without the user’s permission. It usually comes in the form of a malicious link or fraudulent message that tricks people into revealing sensitive information, including credit card numbers and passwords.
- Password guessing: Surprisingly, password guessing is proven to be an effective method for attackers. As unlikely as it may seem, people often use their birthday dates or pet names as password keys, making them easy to crack.
- Password hash cracking: In the majority of current operating systems, any password entered by a user is converted using a cryptographic hash technique into a representative hash (or cipher) of the password. Such hashes are kept in databases used by the operating system to verify users’ identities when they access services or apps. A skilled hacker can figure out how to break the encryption algorithm if they manage to retrieve this hash.
Users should switch to unique and more secure passwords to avoid these data breaches. Of course, the optimal solution would be to switch to passwordless authentication.
Passkeys are still a relatively new technology, and it will take time before we fully adapt to these security measures. But, once this convenient and secure alternative to standard passwords becomes the new normal, the number of data breaches will significantly drop, and the internet will become a slightly safer place for all.